- cross-posted to:
- longreads
- [email protected]
- cross-posted to:
- longreads
- [email protected]
This is a very entertaining and educational article, giving insights into the methods used by thiefs to try and get access to your phone data.
I don’t like Apple but it’s great that their security is so good when it comes to this.


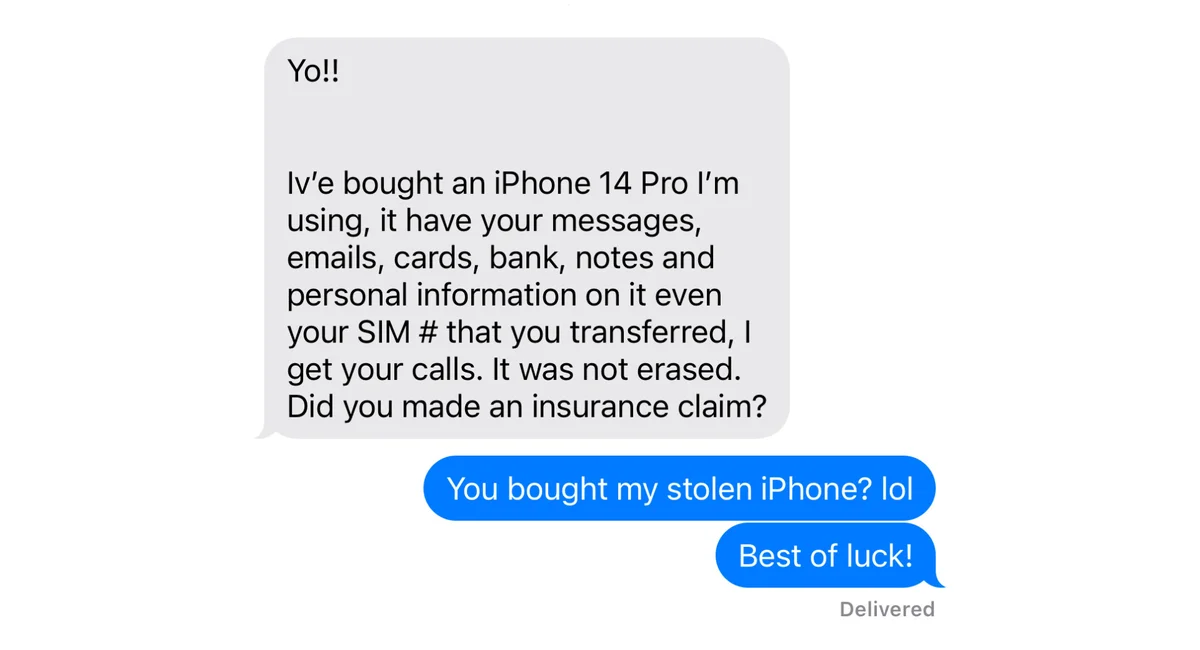
No, its not exclusive. But FRP can be bypassed if you know the right tools.