I’m kinda confused. This looks like really old information re-packaged as some sort of “exploit”. Examining the RDP cache is an old trick. Here’s a video on doing it from six years ago:
https://www.youtube.com/watch?v=NnEOk5-DstwThe tools for doing this, have been out for a long time. Here’s the EnCase tool:
https://marketplace.opentext.com/cybersecurity/content/rdp-cached-bitmap-extractorHere’s an open source parser:
https://github.com/ANSSI-FR/bmc-toolsSo, what’s new here and how is this allowing “Attackers to Take Over Windows and Browser Sessions” other than, if they are on a system, they can dig through the RDP cache? Which, if they are already on the system which launched the RDP sessions, the horse is long out of the barn. Between credential dumping, keylogging and pass the hash, the attacker probably has as much access as the local user has anyway.
Yeah this article is complete garbage. Who upvotes this stuff?
The article is a flat lie. It allows attackers to view fragments of an rdp session screen and nothing else like “take over” anything. It’s also not remotely new.
And here my company ONLY allows RDP for Remote connections, claiming it’s always safer.
are they behind firewalls or vpn?
If you are using regular Windows rdp, you might suggest your business follow the guidelines to minimize the attack vector. At my work we use RoyalTS and it is the bee’s knees. Lots of extra security added in and lots of easy of use.
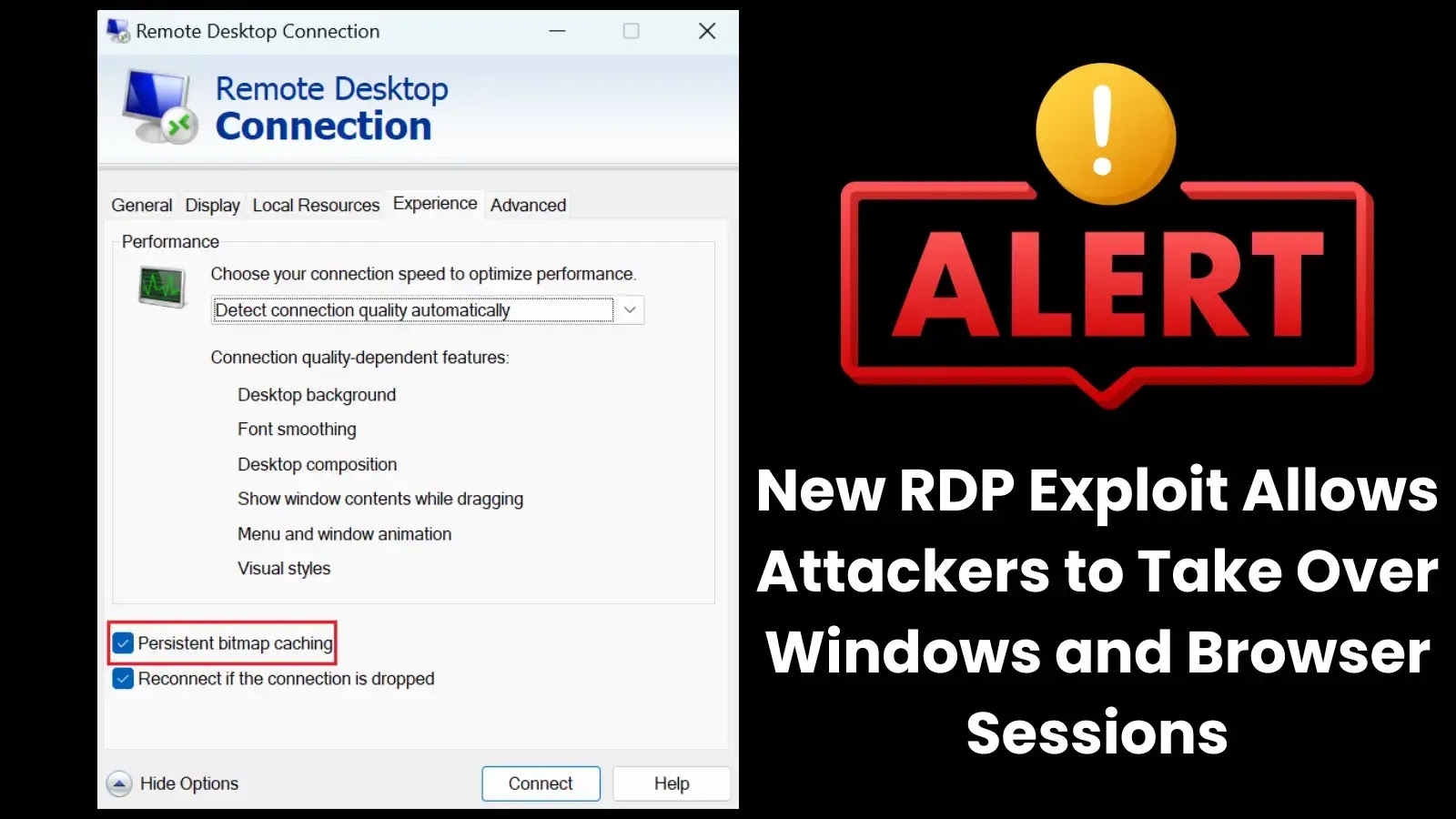
Disable Persistent Bitmap Caching: RDP clients (such as mstsc.exe) allow users to disable bitmap caching, minimizing the exposure of session data. Strengthen Network Security: Employ Virtual Private Networks (VPNs) and robust firewalls to secure RDP connections from external threats. Monitor RDP Sessions: Log and monitor RDP sessions for suspicious activity, including unexpected outgoing connections or file movements. Restrict Privileges: Implement the principle of least privilege to limit unnecessary RDP usage. Apply Updates: Regularly update Windows systems and security patches to prevent exploitation of known vulnerabilities.