- cross-posted to:
- [email protected]
- [email protected]
- [email protected]
- cross-posted to:
- [email protected]
- [email protected]
- [email protected]
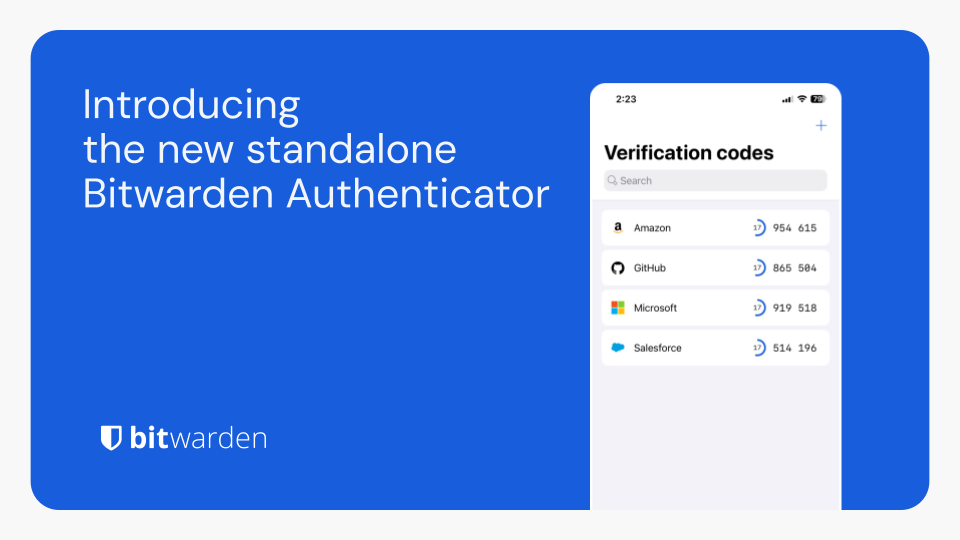
Bitwarden Authenticator is a standalone app that is available for everyone, even non-Bitwarden customers.
In its current release, Bitwarden Authenticator generates time-based one-time passwords (TOTP) for users who want to add an extra layer of 2FA security to their logins.
There is a comprehensive roadmap planned with additional functionality.
Available for iOS and Android


And where would you store your Bitwarden login TOTP if you used their service instead of self hosting?
And what happens if your Bitwarden account gets compromised? Now you’ve lost both factors at the same time.
No, I’ll keep my 2FA separate from my password manager, thank you very much.
Good luck getting your vault compromised.
Unless you have a weak password or the vault isn’t encrypted (which it is, AES256 iirc and you might be able to change that on a self hosted version), I don’t see that happening.
Most password manager hacks don’t attack the encryption or password themselves (my password is very long), they find/create a side channel. For example:
Every secure system can be defeated, but it’s a lot less likely that two secure systems will be defeated at the same time. So I keep my passwords and second factors separate. It’s unlikely that either will be compromised, and incredibly unlikely that both will be compromised at the same time.