cross-posted to: https://sh.itjust.works/post/12856684
I have the following topology:
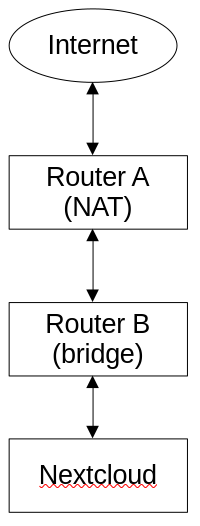
The device running Nextcloud (snap) used to be connected to Router A, but I have recently added a bridge (Router B) and I moved Nextcloud’s device to that bridged network; however, as soon as Nextcloud was moved to Router B, the portforward on Router A seemed to stop working – as in I cannot connect to nexcloud from the public IP anymore. Bridges operate at layer 2, so this should make no difference whatsoever (this is reflected in the fact that other services (like SSH) still work perfectly fine portforwarded – it’s only Nextcloud that doesn’t work), which leads me to think that it is a Layer 7 (i.e. Nextcloud) issue. What’s going on here? How can Nextcloud even tell that it’s been placed on a bridged network?
EDIT (2024-01-16T00:19Z):
I performed a network capture on the device running Nextcloud, and it appears that it’s receiving the incoming request (SYN), and responds appropriately (SYN, ACK), but then Router B responds with Destination unreachable (Network unreachable), which is then, of course, followed by many requests for retransmission as the packets are being dropped. But what’s causing the packets to be dropped? Why aren’t they making it through the network?
EDIT (2024-01-25T08:37Z):
I’m not 100% sure what the previous problem was, but I think that it had to do with the bridge that I was using – not necessarily that it was broken, but perhaps it was jsut incompatible with the setup in some way. What I ended up doing was buying a different router that supported WDS, and then I created a WDS bridge between the two routers. The network seems to be working reliably, and as expected now.

Alright, I now am able to ping a device on Router B from a device on Router A, but I’m still not able to ping a device on Router A from a device on Router B.
Here’s the firewall settings for Router B:
lan zone:
wan zone:
EDIT:
Scratch that! apparently it is working. I could’ve sworn that I checked the ping. Maybe I subconciously applied something else.